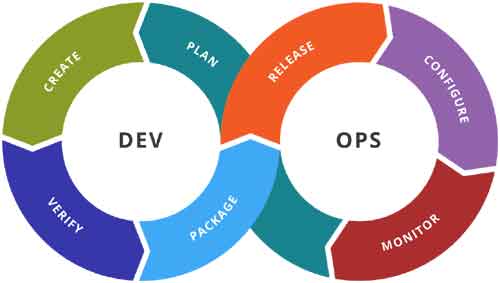
Beginners Guide to DevSecOps Security – DevOps Model
Guide to DevSecOps Security Discussing the DevSecOps security model and its aim, implementation, or process….
Mac Maintenance Tips to Boost your Business Security
Mac Maintenance Tips macOS devices are integrated with tight inbuilt security features that make them…
Secure Cloud Data: 3 Ways to Keep Your Data Safe on the Cloud
Secure Cloud Data Discussing different ways to secure cloud data. Is the information you store…
Create A Data-Driven Organization: Here Are 5 Ways You Can Do So
Create A Data-Driven Organization Do You Want To Create A Data-Driven Organization? Are some ways,…
Why Dedicated Server? Best USA Dedicated Server Plan
Best USA Dedicated Server Plan Considering the best USA Dedicated Server Plan at Low Cost….
How to choose the appropriate Laptop protection plan
Laptop protection plan In modern times, almost everything you do is dominated by computers. In…
The Advanced Tools to Secure Data Transfers Remotely
Tools to Secure Data Transfers Discussing the most advanced tools to secure data transfers while…
Family Security App – Control your Child’s Social Media Usage
Family Security App Discussing the family security App for controlling the child’s internet usage. In…
When Should You Use Data Center Proxies
Data Center Proxies In this article, we shall focus on data center proxies and their…
Top 7 factors to focus on when Website Security is First Priority
Website Security is First Priority As we move ahead with technology, the dark web rears…