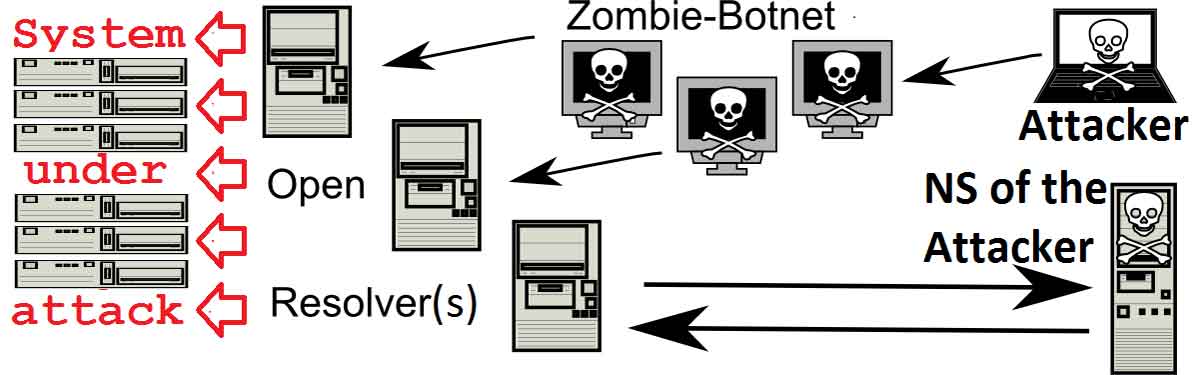
What Is a Botnet Attack – Detection and Protection Tips
What Is a Botnet Attack? Botnet attacks are a grave kind of cyber attack. A…
Why do you need an access control system for your business?
Using an access control system We defined an access control system as a system of…
4 Cybersecurity Threats Lies on the Front Lines of Businesses
Exploring top cybersecurity threats lies on the front lines of businesses today. During the wake…
7 Best Practices to Secure Your Business Network
Secure Your Business Network In this modern digital era, it is next to impossible to…
What is Network Security – Why Should You Invest in it
With cybercrime on the rise, your small business is becoming more and more at risk…
Thinking to open a Cyber Security Venture: Aspects to consider
Cyber Security Venture Deeming to open a Cyber Security Venture, here are the aspects to…
Managed IT solutions let you keep up with the digital world! How?
Managed IT Solutions for IT Needs With developing technology and recent developments, you know the…
How to demonstrate your Data & Document Security Solutions
Data and Document Security Solutions Almost every organization views data and document security solutions as…
How Digital Payment Solutions Can Drive Business Revival
How digital payment solutions can drive a business revival in the new normal. The impact…
10 Factors Driving Businesses For adopting Managed IT Services
Adopting Managed IT Services Discussing the factors that drive small businesses for adopting managed IT…